See Your OT Attack Surface Before Attackers Do
ShiftSix continuously discovers internet-exposed industrial assets using passive, outside-in reconnaissance. See your infrastructure the way an adversary does, without touching your network.
Latest Research
View all →The OT Perimeter Problem
Why firewalls and VPNs are the #1 source of OT internet exposure.
Read more → OT ExposureThe Myth of the OT Air Gap
How "air-gapped" OT networks end up internet-exposed through VPNs, cellular, and cloud misconfigurations.
Read more → Protocol AnalysisWhen Modbus Meets the Internet
What attackers can do when Modbus/TCP is reachable from the internet.
Read more →Attackers Don’t Hack In. They Buy Access.
Initial Access Brokers scan the internet for exposed OT assets, gain a foothold, and sell that access to ransomware operators and nation-states. The entry point is almost always an asset the organization didn’t know was exposed.
Automated scanners sweep the internet at 36,000 scans per second, probing for open Modbus, DNP3, and OPC UA ports. New assets are discovered within 5 minutes of going online. OT-focused groups like SYLVANITE specifically target edge devices from Ivanti, Fortinet, and F5. These are the same VPN appliances protecting your OT perimeter.
145,000+ ICS services exposed across 175 countries. 46,000+ devices communicating over Modbus on the open internet.
Censys 2024 · Dragos 2026Access brokers exploit exposed VPNs, forgotten engineering workstations, and shadow OT connections that were never inventoried. 70% of access sold on dark web forums is VPN or RDP credentials, often from the same Fortinet and Ivanti appliances sitting at your OT perimeter. The average listing costs $2,047. Critical infrastructure commands premiums above $10,000.
76% of organizations have been attacked through an asset they didn’t know was internet-exposed. 38% of all breaches trace to unknown or unmanaged assets.
ESG / Palo Alto · IBM 2024Compromised access is sold to ransomware affiliates on forums like XSS and RAMP, or handed directly to nation-state Stage 2 operators like VOLTZITE. Dragos documented SYLVANITE handing off compromised OT environments to destructive actors within days. Mandiant measured the average handoff collapsing from 8+ hours in 2022 to 22 seconds in 2025.
119 ransomware groups targeted 3,300 industrial organizations in 2025. 50% of all ransomware attacks hit critical infrastructure sectors.
Dragos 2026 · Industrial CyberRansomware deploys. Operations halt. The average breakout time from initial access to lateral movement is 29 minutes. Fastest observed: 27 seconds. FrostyGoop connected directly to internet-exposed Modbus controllers from Moscow, cutting heat to 600 Ukrainian households. No prior network compromise needed. The device was simply exposed.
Unauthorized external access accounted for 50% of all OT incidents. Average industrial breach cost: $5.56M , 13% above the global average.
SANS 2025 · IBM 2025ShiftSix runs the same reconnaissance playbook as Initial Access Brokers —
but we report to you, not to ransomware operators.
Organizations prioritizing CTEM are 3× less likely to suffer a breach. Gartner set the timeline for 2026. that year is now.
Gartner, Implement a CTEM Program, July 2022
What attackers see → What matters most → What gets fixed
From outside-in discovery to closed exposure. Continuously, without touching your network.
Only 12.6% of organizations have full ICS Kill Chain visibility. ShiftSix gives you the outside-in perspective most teams are missing entirely.
SANS 2025 ICS/OT Survey
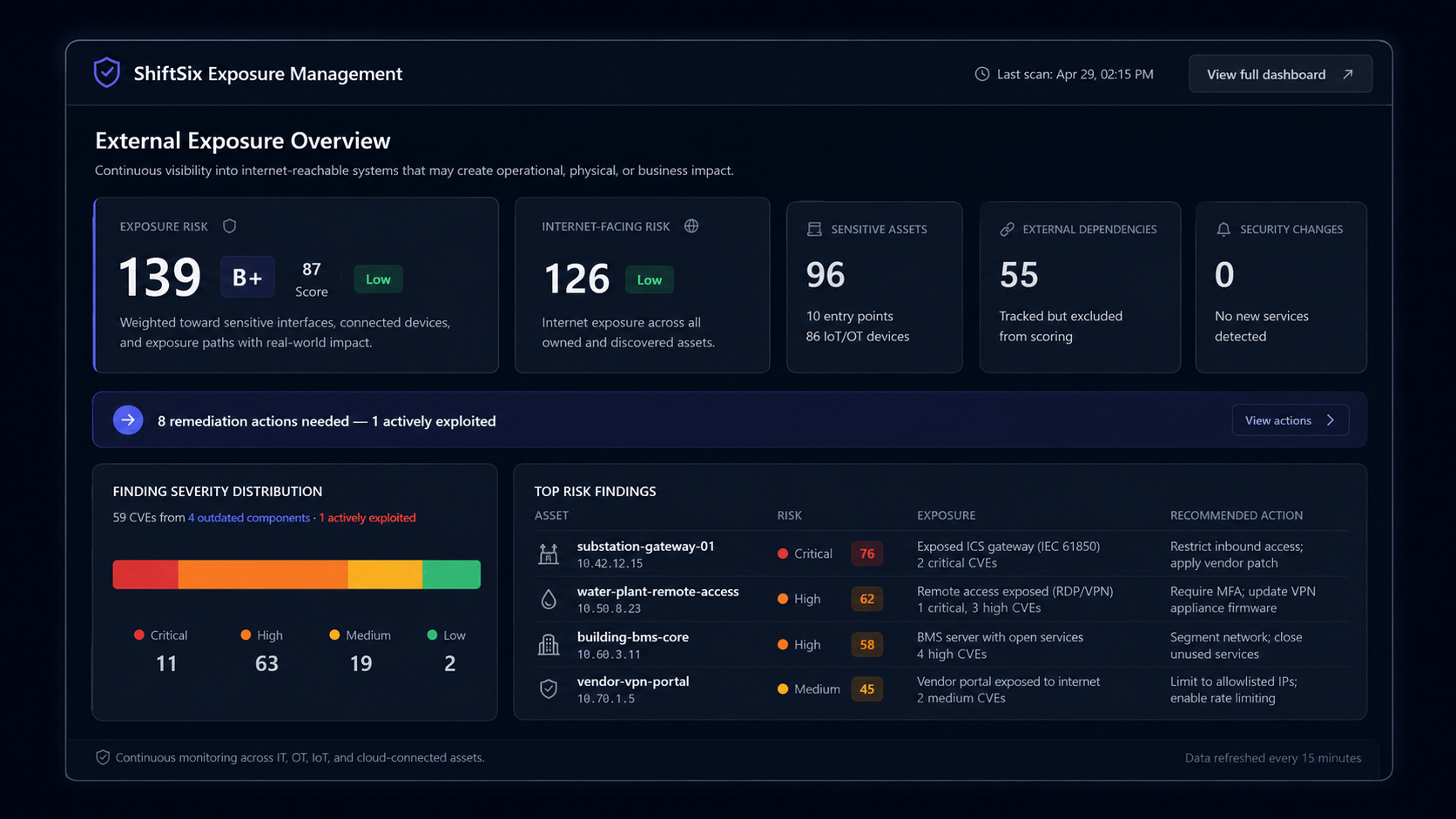
Discover Your Exposure
See what SYLVANITE’s scanners already see, before they sell it.
Passively identify every internet-exposed OT asset across your infrastructure. No agents, no sensors, no network changes. Results in hours, not months.
5 protocols · 175 countries · 0 packets sent
Prioritize by Real Threat
Not every exposure becomes a $2,047 listing. Know which ones will.
Map each exposure against active threat actor TTPs and ICS-specific malware. Not theoretical CVSS scores. 38% of OT CVSS scores contain errors. We skip the noise.
12 ICS malware families · 47 active threat actor TTPs
Close & Verify
Remove the exposure before it becomes a listing. Verify it stays gone.
Deliver remediation guidance contextualized to your OT environment. Continuously verify exposures are removed from the live attack surface. Not quarterly. Continuously.
Continuous verification. Not quarterly, not annual
See What Attackers See
Your internet-exposed OT assets, scored by severity, mapped to compliance frameworks, and benchmarked against your industry. Delivered in 24 hours.
Ransomware groups (Qilin, Play, Akira) and nation-state campaigns like VOLT TYPHOON and FrostyGoop that are actively targeting your sector.
Maps your external attack surface against known IAB reconnaissance patterns and initial access playbooks.
Prioritized by real-world exploitability, not CVSS scores. Written by OT threat researchers, not algorithms.
Every internet-visible PLC, RTU, HMI, and protocol gateway identified with geolocation, ownership attribution, and banner analysis.
100% passive · No agents · No network access required
ShiftSix vs. OT Network Monitoring Platforms
Claroty and Dragos monitor traffic inside your OT network. ShiftSix shows you what attackers see from the outside before they get in. They are complementary, not competing.
| ShiftSix | Claroty | Dragos | |
|---|---|---|---|
| Approach | Outside-in (CTEM) | Inside-out monitoring | Inside-out monitoring |
| Sensors or agents required | ✓ None | Multiple (sensors, agentless, active queries) | Passive sensors (active collection optional) |
| Touches your OT network | ✓ Never | Passive tap + active queries | Passive tap |
| Attacker-perspective visibility | ✓ Yes | No | No |
| CISA KEV correlation | ✓ Native | Native | Limited |
| Deployment | SaaS (no hardware) | SaaS + On-prem | SaaS + On-prem |
| Primary use case | Pre-breach exposure visibility | Network monitoring + exposure management | Network monitoring + vulnerability management |
Already using Dragos or Claroty? ShiftSix is complements your existing OT monitoring stack. We show you what is visible from the internet before threats reach the network your monitoring tools protect.
Common Questions
What is Continuous Threat Exposure Management (CTEM)?
Continuous Threat Exposure Management (CTEM) is a cybersecurity framework defined by Gartner in 2022 that continuously scopes, discovers, prioritizes, validates, and mobilizes remediation of security exposures. Unlike point-in-time assessments, CTEM runs as an ongoing cycle. This is critical for OT and ICS environments where new exposures emerge daily. ShiftSix operationalizes CTEM into three steps: Enumerate, Correlate, and Close.
What is OT Exposure Management?
OT Exposure Management is the process of continuously discovering and prioritizing internet-exposed operational technology assets : PLCs, RTUs, HMIs, and protocol gateways, from outside the network. Unlike internal vulnerability management, OT Exposure Management operates from the adversary perspective, mapping what attackers can reach before they exploit it. ShiftSix scans 60+ industrial protocols passively, with zero agents or network access required.
How is ShiftSix different from Claroty or Dragos?
Claroty and Dragos are OT network monitoring platforms that provide inside-out visibility into traffic and behavior within your industrial network. ShiftSix is an OT-native CTEM platform that provides outside-in exposure intelligence, mapping what attackers can reach from the internet before they ever reach your OT network. ShiftSix requires no agents, no scan windows, and never touches your OT network. It is complements existing OT monitoring tools, not replace them.
How does ShiftSix map to regulatory and industry frameworks?
ShiftSix maps discovered external exposures against NERC CIP, IEC 62443, NIST CSF 2.0, NIS2, MITRE ATT&CK for ICS, and CISA ICS-CERT advisory frameworks, giving operators audit-ready evidence alongside their exposure data. This reduces manual evidence-gathering overhead and gets audit documentation ready before the auditor arrives.
Does ShiftSix require any changes to my OT network?
No. ShiftSix operates entirely from the outside in using passive reconnaissance: certificate transparency logs, service banner analysis, protocol fingerprinting, and DNS enumeration. We never send packets to your network, never require agents or sensors, and never need network access. Your OT operations continue completely uninterrupted. Most organizations receive their first exposure map within 24 hours.
Why should I care about external OT exposure specifically?
Because attackers start from the outside. Forty percent of organizations have vulnerable OT assets insecurely connected to the internet (Claroty 2025), and the average cost of an industrial breach is $5.56 million, 13% above the global average (IBM 2025). Unplanned OT downtime costs $125,000 per hour. External exposure is the first link in the kill chain, and it is the one most OT security programs overlook because their tools are designed for internal visibility.
LATEST RESEARCH
Exposure Management
The OT Perimeter Problem: Why Firewalls & VPNs Are the #1 Attack Vector
67% of malicious OT activity targets perimeter devices.
OT Security
The Air Gap Is a Diagram, Not a Defense
40% of OT environments are directly internet-connected.
Threat Intelligence
What Happens When Modbus Is Exposed to the Internet
54,000+ Modbus devices sit exposed with zero authentication.
Your OT Attack Surface Is Already Mapped. By Someone.
Every day your internet-exposed OT assets sit unmonitored, attackers are mapping them. Nation-state OT attacks nearly doubled in 2025. ShiftSix shows you exactly what they see so you can close it before they exploit it.
Get your free exposure report in under 24 hours. No agents, no sensors, no sales call.
